The world’s biggest tech company suffered a massive cyberattack on Nov. 12 that redirected web traffic through Russia, China, and Nigeria, and disrupted Google services such as search, cloud storage, and G Suite functions.
According to the Associated Press (AP), the attack placed “valuable Google traffic in the hands of ISPs [Internet service providers] in countries with a long history of Internet surveillance,” AP cited ThousandEyes, a network-intelligence company, as saying.
In addition to Chinese and Russian networks, traffic was also rerouted through a major ISP in Nigeria, where the cyberattack began and within minutes spread to the other countries involved. Service interruptions at Google lasted about an hour and a half, ending around 5:30 p.m. EST.
Sites like YouTube and Twitter were malfunctioning or down during the attack.
Following the attack, Google offered few details, saying on its status page that some services had been impacted due to a cause “external to Google.” AP reported that “Google said it had no reason to believe the traffic hijacking was malicious. It did not explain why.”

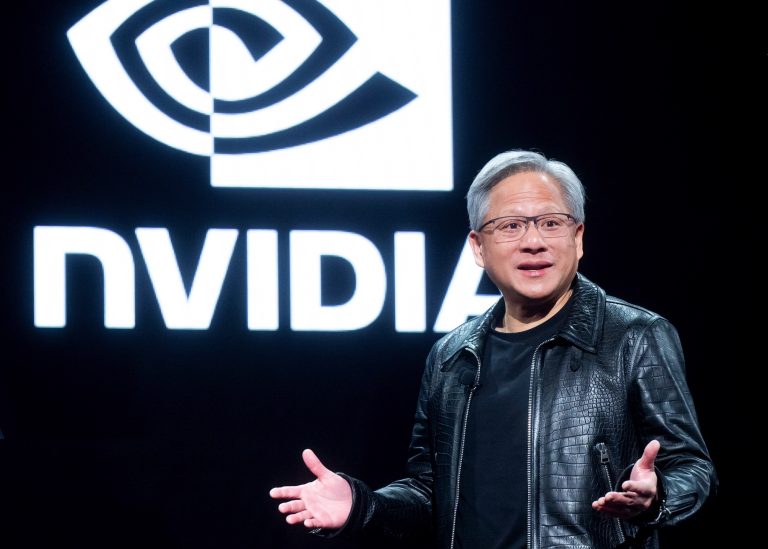
Google, the world’s biggest tech company, suffered a massive cyberattack on Nov. 12. (Image: Downdetector.com / OpenStreetMap)
Success
You are now signed up for our newsletter
Success
Check your email to complete sign up
Alex Henthorn-Iwane, an executive at ThousandEyes, which is based in San Francisco, told AP that the incident was the worst attack they’d ever seen carried out against Google. He said it was likely that foreign governments had had a hand in the attack, since Google’s data was being effectively funneled to Beijing’s state-run China Telecom.
China frequently carries out cyberattacks to divert U.S. internet traffic, according to a recent study published by the U.S. Naval War College and scholars at Tel Aviv University in Israel.
Last month, a breach of the now-defunct Google+ social network exposed the private data of about half a million people.
Hawthorne-Iwane said the Nov. 12 attack could be a “virtual wargame.”
Traffic misdirection is also known as border gateway protocol (BGP) hijacking. It can knock essential services offline and facilitate espionage and financial theft. Misdirection can be a result of either human error or malicious action.
While the vast majority of data sent via Google services is encrypted, governments of countries that the traffic is diverted through can gather metadata from it — such as who sent the data, to whom it was sent, or over what timeframe.
Gathering metadata can help repressive governments, such as the Chinese Communist Party, track down dissidents who use Western social media services. The CCP has recently managed to delete the Twitter accounts of prominent Chinese activists, who use the site by using special software to circumvent government censors.

Gathering metadata can help repressive governments, such as the Chinese Communist Party, track down dissidents who use Western social media services. (Image: pxhere / CC0 1.0)
Apart from China Telecom, the Nov. 12 attack rerouted data through Russia’s TransTelecom and ISP MainOne, a Nigerian ISP.
“Google network traffic normally travels through vetted service providers. A U.S.-based Chinese “Point of Presence” (PoP) — a legal Internet access point that allows Chinese citizens to access U.S. sites — intercepted this data and sent it to China Telecoms,” according to the UK-based Daily Mail.
Professor Alan Woodward, a computer scientist at the University of Surrey, told the Daily Mail: “The hijack could have been part of an elaborate surveillance scheme.” He said: “Access to people’s data is a ‘strategic asset’ for surveillance, and Russia and China have carried out hijack attacks to collect that data before.”
China Telecom has significant partnerships with North American communications networks. It has 10 PoPs across the continent — two in Canada and eight in the United States. Chris Demchak of the United States Naval War College and Yuval Shavitt of the Tel Aviv University in Israel have traced global border gateway protocol (BGP) announcements and revealed that China Telecom had carried out several attacks in the past few years, according to reports in Secure Reading, the Daily Mail reported.
TransTelecom, which is run by the Russian government’s railway operator, has been providing North Korea with Internet connectivity since at least 2017, when analysts discovered the link. Along with China, North Korea has a well-developed cyberwarfare unit that has been implicated in several major cyberattacks.
Google and other large tech companies have been criticized for tacit cooperation with the Chinese communist authorities.
In September, insider information revealed the existence of a secret Google project, codenamed “Dragonfly,” that would provide mainland China with a censored version of the search engine that is ubiquitous among Internet users in the United States and other parts of the world. Google is currently banned in mainland China
Last year, the Party forced Apple to move its Chinese regional servers to mainland China, effectively turning over to the CCP the private data of all users who set their region to “China,” regardless of whether they are actually located on the mainland or not.
Follow us on Twitter or subscribe to our weekly email