Google has removed several spyware-containing apps from its AppStore after an international data scam involving shadowy offshore companies, tens of millions of end-users, and links to the U.S. Defense Department emerged.
At least a dozen apps turned out to be infected with code harvesting millions of Android users’ confidential data and location tracking, two researchers, Serge Egelman of the International Computer Science Institute and the University of California, Berkeley, and Joel Reardon of the University of Calgary, wrote.
The pair found that code was developed by a Panama-registered company called Measurement Systems S. de R.L. whose web domain was registered by a U.S.-based firm called Vostrom which, in turn, had close ties with a Virginian Defense contractor specialized in cyber-security, Packet Forensics LLC, research shared by the Wall Street Journal, revealed.
READ MORE:
- The Revenge of the Dumbphone
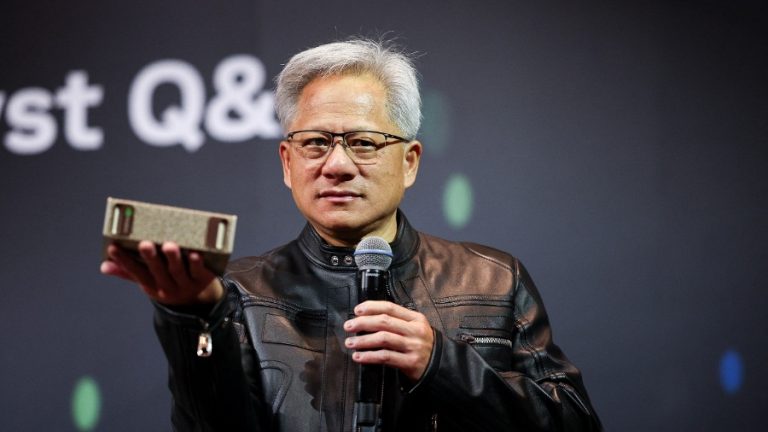
- Consumer Electronics Demand Down ‘Especially in China’ Says TSMC Chief
- This Social Credit-Style Digital Currency App Tracks User Eye Movements to Ensure Ads are Watched
The spyware was encapsulated as a software development kit (SDK) and is offered to software developers from the angle of an alternative form of monetization.
Several apps, such as a Muslim prayer app, a QR-code reader, a highway-speed trap detection snitch app, and many others utilized the SDK. Measurement Systems told prospective devs they could earn between $100 and $10,000 a month, depending on their userbase, the report said.
Far reaching eavesdropping skills
Success
You are now signed up for our newsletter
Success
Check your email to complete sign up
The SDK also made it possible for data miners to collect sensitive user credentials, such as passwords, as it harvested data stored on the user’s clipboard and accessed specific internal files, such as those contained in the storage folders for popular chat and communications app WhatsApp.
On top of that, Measurements Systems was able to simultaneously gain access to a user’s exact location data and personal identifiers, such as email addresses and phone numbers.
Furthermore, the spyware contained the ability to spy on nearby devices’ data once connected to the same wireless network router Reardon, and Egelman found.
“A database mapping someone’s actual email and phone number to their precise GPS location history is particularly frightening, as it could easily be used to run a service to look up a person’s location history just by knowing their phone number or email, which could be used to target journalists, dissidents or political rivals,” Reardon said in a blog post cited by WSJ.
In March, before going public with the results, the duo informed Google, upon which the tech giant launched its own investigation and removed tens of apps infected with the code from its AppStore.
However, Google’s ban on the infected apps won’t protect those users with the app already installed on their phones from being spied on.
Only after the two scientists disseminated their conclusions to the press did they find out that the SDK had stopped working and deactivated itself.
Similar cases
In February, Vision Times covered the story of how a data broker, formally known as X-Mode, sold millions of dollars worth of sensitive location data harvested from dating apps and Muslim prayer apps to federal agencies is now owned by a federal government contractor.
X-Mode bought location data from apps like Bro, a dating app for “bi, gay, and open-minded men,” Perfect365, a virtual makeup app, and Tango, a popular live-streaming app, as well as from dozens of other apps that shared their customers’ credentials in what was described as a multibillion-dollar location data trade.
According to The Markup, the acquired data would then be sold to federal agencies such as the Internal Revenue Service (IRS) and Department of Homeland Security.
In December, Facebook parent company Meta banned seven alleged surveillance-for-hire companies from its platforms after those parties installed spyware on end-users’ phones, mining their confidential data, hacking their devices, and selling their data to rogue countries.
Meta claimed it had identified seven cyber mercenary companies targeting 48,000 clients in over 100 countries. Moreover, Meta says it removed 1,500 Facebook and Instagram profiles that could be traced back to these outfits.
In most cases, these firms would create fake profiles to be used as a front which would then be used to collect customers’ intelligence, hack their devices or grab their money.