Meta has banned seven alleged surveillance-for-hire companies from its platforms after those parties installed spyware on end-users’ phones, mining their confidential data, hacking their devices, and selling their data to rogue countries.
Meta, the parent company of social media brands Facebook, Instagram, and WhatsApp reported its purification operation took months of investigation.
Meta claims it has identified seven cyber mercenary companies that have targeted some 48,000 clients in over 100 countries. Moreover, Meta says it removed 1,500 Facebook and Instagram profiles that could be traced back to these outfits.
In most cases, these firms would create fake profiles to be used as a front which would then be used to collect customers’ intelligence, hack their devices or grab their money.
The Meta release authored by David Agranovich, Director, Threat Disruption, and Mike Dvilyanski, Head of Cyber Espionage Investigations put it as follows:
Success
You are now signed up for our newsletter
Success
Check your email to complete sign up
“The global surveillance-for-hire industry targets people to collect intelligence, manipulate and compromise their devices and accounts across the internet.
“While these “cyber mercenaries” often claim that their services only target criminals and terrorists, our months-long investigation concluded that targeting is in fact indiscriminate and includes journalists, dissidents, critics of authoritarian regimes, families of opposition and human rights activists.
“We disabled seven entities who targeted people across the internet in over 100 countries; shared our findings with security researchers, other platforms and policymakers; issued Cease and Desist warnings; and also alerted people who we believe were targeted to help them strengthen the security of their accounts.”
Of the seven surveillance-for-hire businesses, four were believed to have operated from Israel, namely Cobwebs Technologies, Cognyte, Black Cube, and Bluehawk CI, while another one listed as BellTroX was based in India.
Yet another one named Cytrox was registered in North Macedonia. Also, an unidentified firm from China was believed to be engaged in providing spying services on minority groups like the Uyghur minority in China.
Three phases of corruption
Meta said it has “observed three phases of targeting activity by these commercial players that make up their ‘surveillance chain’: Reconnaissance, Engagement, and Exploitation.” Most enterprises were involved with two or all three phases in the process, the report said.
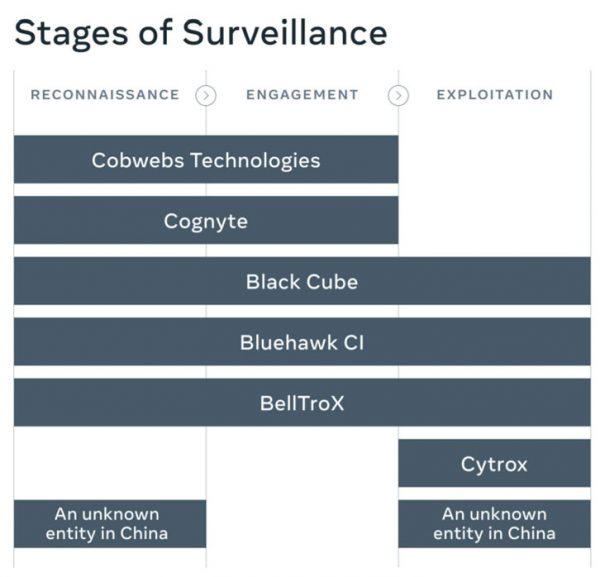
Reconnaissance is typically the phase where targets are being silently profiled by cyber-surveillance companies employing automated data collection tools against internet sources like blogs, social media, and knowledge management platforms like Wikipedia and Wikidata.
The engagement phase is where the surveillance firm is trying to create contact with its targets, build trust, often under the guise of a fake profile, and request data, and deceive them into clicking on malevolent links or files.
The final phase, exploitation, also referred to as “hacking for hire,” is the stage where targeted individuals have already given away vital data like passwords, and PIN codes to access email, social media, and financial services. By that time, their devices will be severely hijacked and irreversibly compromised.
Black Cube, one of the alleged hacking companies, proclaimed innocence, stating in a statement to NPR, that it “does not undertake any phishing or hacking and does not operate in the cyber world.” It identifies itself rather as a “litigation support firm” that follows legal guidelines in its operations.
“Black Cube obtains legal advice in every jurisdiction in which we operate in order to ensure that all our agents’ activities are fully compliant with local laws,” it said.
The highest bidder gets served, indiscriminately
The Meta statement also brings up another case, that of a malware party that Meta banned from its platform in July; Israel-based NSO, a company that provided surveillance services on high profile individuals, like French president Emmanuel Macron, King Mohammed VI of Morocco, and the Dalai Lama.

READ MORE: Israeli Pegasus Spyware Spied on Macron, Dalai Lama, Telegram Founder
However, the Meta report stated, NSO “is only one piece of a much broader global mercenary ecosystem,” part of a “sprawling” yet gloomy industry that offers spying-on-demand services to anyone willing to pay, “regardless of who they target or the human rights abuses they might enable.”
“The surveillance-for-hire industry looks like indiscriminate targeting on behalf of the highest bidder,” Nathaniel Gleicher, head of security policy at Meta, said in a Threat Report that came together with the notice. The goal is to “spy on people or snoop on them without them knowing about it.”
Gleicher told the outlet that those firms were “indiscriminate” about whom they targeted. “We are seeing politicians. We’re seeing human rights activists. We’re seeing lawyers, doctors, clergy, in some cases, ordinary citizens. Anyone who might be party to a lawsuit,” he added.
“Almost every autocrat and dictator around the world is being pitched this kind of technology for surveillance,” Citizen Lab senior researcher John Scott-Railton told the newspaper.
“It’s really important that we get to a place where there are big global norms and regulations around this kind of technology,” Scott-Railton added. “Otherwise, it’s just gas on the authoritarian fire.”
Recommendations
The Meta report concludes by providing recommendations on preventing malevolent malware firms from spying on naive web users, collecting their credentials, turning their phones into spying devices, and selling their sensitive data to rogue regimes.
They entail greater transparency and oversight. “Know your customer” standards should be installed, and surveillance-for-hire firms should be held accountable.
More industry collaboration and information exchange would be other tools to analyze malicious entities’ modes of operation and thwart their efforts whenever possible.
Meta also pleads for an enhanced ethical standard to be observed by law enforcement and private companies and to create effective victim protection regimes.













