On Dec. 18, the U.S. Department of Justice unsealed a complaint and arrest warrant against Xinjiang Jin, an employee of U.S.-based Zoom who worked out of the company’s mainland China offices. Jin, who goes by the name Julien, was charged with Conspiracy to Commit Interstate Harassment and Unlawful Conspiracy to Transmit Means of Identification.
The investigation, which was conducted by the FBI’s Washington Field Office, fully acknowledges Zoom’s operations within Communist China: “[Zoom] has significant operations in the People’s Republic of China (‘PRC’) where it employs hundreds of workers who primarily focus on research and development.” The Chinese Communist Party’s (CCP) wanton censorship of speech, especially dissent, is core to the charges against Jin: “…the CCP regards any political dissent as a threat not only to its own political interest, but also to the PRC’s one-party system of government itself.”
“To effectuate this censorship scheme, the PRC government requires electronic communications service providers that operate in the PRC, such as [Zoom], to proactively monitor users’ activities on their networks and to terminate discussions of politically sensitive topics.” The CCP also requires companies that operate within China to “respond immediately when a PRC national security or law enforcement agency demands that the service provider terminate a discussion of a politically sensitive topic.”
‘Pretextual justifications’
The complaint reveals how the CCP uses the continual threat of its “Great Firewall of China” to block Internet connectivity to companies who fail to give the Party what it wants.
Jin was a “Security Technical Leader” at Zoom’s Zhejiang branch where his role was “serving as primary liaison with PRC authorities, including law enforcement and intelligence services.” Jin targeted individuals residing in the United States, several of whom held active subscriptions with Zoom and whose calls were hosted on U.S. servers. In fact, Zoom’s platform was used as a tool for Jin to carry out his tasks at the request of the CCP.
Success
You are now signed up for our newsletter
Success
Check your email to complete sign up
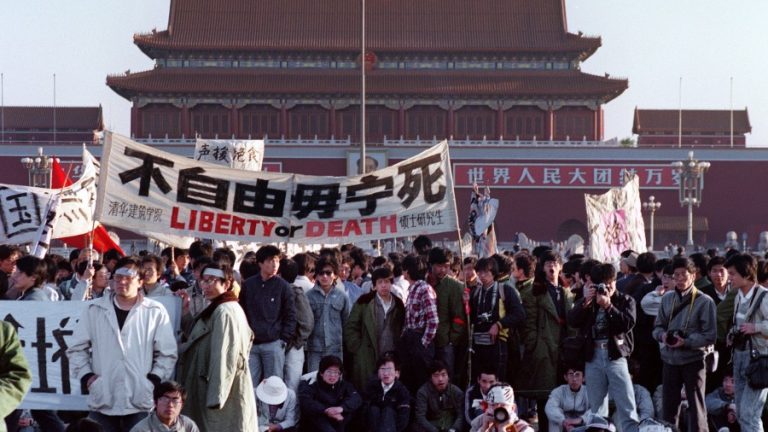
The complaint alleges that Jin “and his co-conspirators fabricated evidence of TOS (terms of service ) violations to provide pretextual justifications to terminating the meetings, as well as certain participants’ accounts,” and that the FBI is in possession of messages from Jin to other Zoom employees about his efforts to harvest intelligence from social media on Zoom’s clients who were planning events that commemorated the June 4, 1983, Tiananmen Square Massacre.
Jin primarily worked with a “high-ranking employee of [Zoom] in the United States… to effect the termination of meetings and the suspension and cancellation of user accounts.” This high-ranking U.S. employee is referred throughout the Complaint as “Employee-1.”
In one account, Jin spearheaded an effort to create fake Zoom accounts with profile pictures related to terrorism and pornography. These accounts entered the meetings Jin wanted to have a pretext to take down. Then, Jin and his conspirators screenshot their own actions and claimed the meetings were violating Zoom’s Terms of Service.
The complaint also documents an event in May where a dissident who “participated in Hong Kong politics as a pro-democracy activist” had their account terminated in advance of scheduled meetings that Jin and Employee-1 called “political.” Users hosting meetings with religious themes were targeted at Jin’s sole discretion as well. In one such case, Employee-1 both terminated a user’s account and provided Jin with their IP address and metadata information. The user’s IP was traced to China’s Yunnan Province.
Despite Jin and his alleged co-conspirators’ efforts, the CCP was not satisfied.
The Party then used its ability to completely censor and control the Chinese Internet to block Chinese connections to Zoom in September of 2019. Zoom was forced to meet with CCP officials and was told they could only resume operations if they complied with Party regulations.
Shut down in China
Zoom confirmed in a Dec. 18 blog post in response to the unsealing of the DOJ complaint that they had been blocked by the CCP: “In September 2019, the Chinese government turned off our service in China without warning… The shutdown caused significant disruption for many of our multinational customers, who could not effectively communicate with their employees and partners in China… They urged us to take immediate action to get the service resumed.”
The complaint specifically mentions a “rectification” plan being discussed between Jin and Zoom employees between October of 2019 and June of 2020. The plan required Zoom to “proactively monitor” its platform for content the CCP feared, with Jin being made the “primary liaison” between Zoom and the Party. This was confirmed by Zoom’s blog post: “in October 2019, Zoom appointed the now-former employee to serve as the government contact in China. This former employee’s job included responding to the Chinese government’s requests for account terminations, meeting terminations, and user data.”
Zoom was required, under the plan, to “migrate the data storage” of more than a million U.S.-based “Chinese users” to servers controlled by the Party. In addition, Zoom was instructed to provide CCP agents with “special access” to Zoom’s systems. Jin claimed in messages to employees that Zoom’s CEO had agreed with the Ministry of Public Security (MPS) to use a combination of Zoom and WeChat to communicate with CCP officials when exchanging classified information. According to messages by Jin in the complaint, Zoom was unblocked by the Party in November of 2019.
When the CCP Virus pandemic took global effect in early 2020, much of the world’s population was forced to work from home, with governments around the world using the pandemic as an excuse to implement increasingly strict lockdowns. Zoom’s usage, and its stock price, skyrocketed. The complaint alleges that the CCP took advantage of this opportunity to “impose additional controls” on Zoom’s platform and demanded a “policy of immediate remediation of any illegal conduct.”
The Ministry of State Security (MSS) told Jin they didn’t want Zoom to terminate meetings held by targets immediately. First, they wanted to use the opportunity to observe and collect intelligence on participants and the contents of their discussions. In no uncertain terms, the CCP was spying on Zoom’s clients and Zoom gave the Party both the tools and the wherewithal to do so.
Enough is never enough
But when it comes to being in cahoots with China’s red dynasty, enough is never enough.
In April 2020, Jin was summoned by CCP officials. Later, he told Employee-1 that the Communist regime instructed them to develop the ability to “respond to a PRC demand” to terminate a meeting, account, or recording within one minute. Jin dubbed this the “one-minute processing requirement.” Employee-1 connected Jin to another U.S. based employee who could provide him with access to a remote machine, located on U.S. soil, that was connected to Zoom’s U.S. operations. This was to allow Jin to comply with demands from the MPS and MSS. According to the Complaint, Employee-1 ordered this employee to comply with Jin.
Jin boasted about CCP infiltration in the United States in electronic messages with Zoom’s staff, saying the “CCP infiltrated the United States, and, even if [Zoom] withdrew entirely from the PRC, [Zoom] would still need to deal with ‘CN zf’ [shorthand for China Zhengfu, or Chinese Government] requests in order to avoid future attacks.”
There was one continuous thread driving Jin and the CCP’s agents behind him: a ploy to convince U.S. employees to acquiesce to his ever-escalating demands under their threat to block Zoom’s services with the Great Firewall. In June, Jin received, upon request, a spreadsheet containing approximately 23,000 user IDs and account IDs for Zoom accounts directly from a Zoom employee.
The Complaint does not make note of any resistance to this pressure from either Zoom or Employee-1. They seem to have preferred to assume the risk of their actions over the prospect of losing the business opportunity inherent in the Chinese market.
According to Zoom’s blog post, the company states it has terminated Xinjiang Jin’s employment and placed all other employees involved on administrative leave pending the completion of the investigation. Xinjiang Jin is not currently in U.S. custody and is now on the FBI’s Most Wanted List. If he is captured and convicted of both counts, he faces a maximum of 10 years in prison.
Follow us on Twitter or subscribe to our email list